-
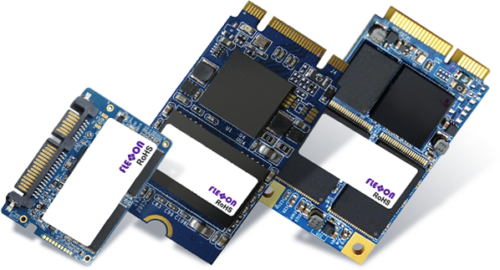
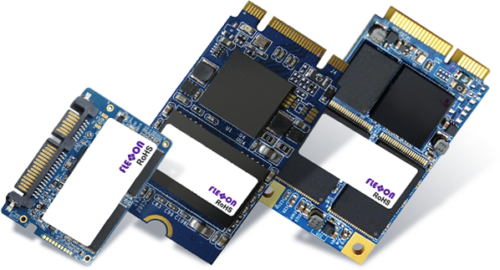
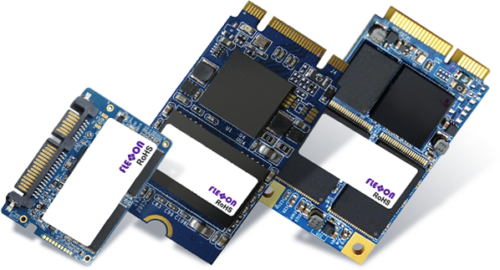
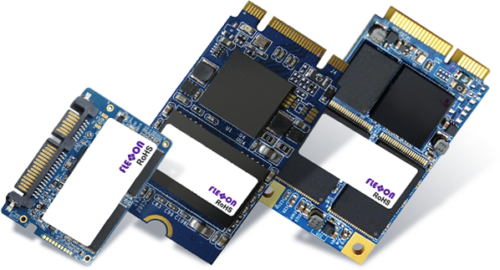
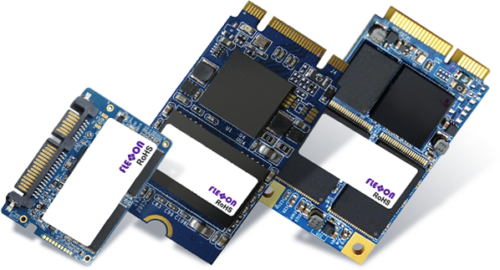
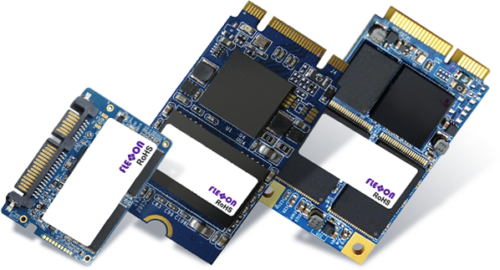
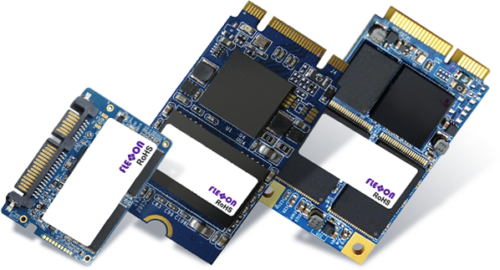
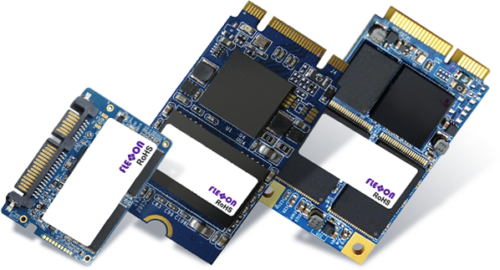
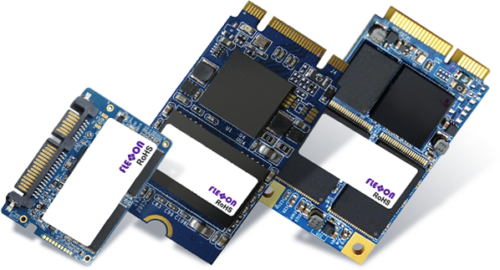 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
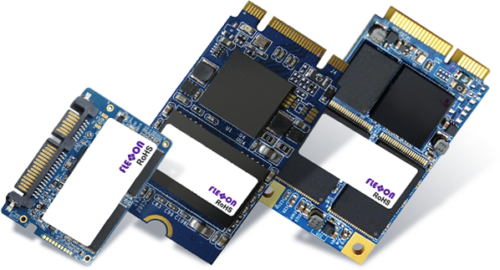
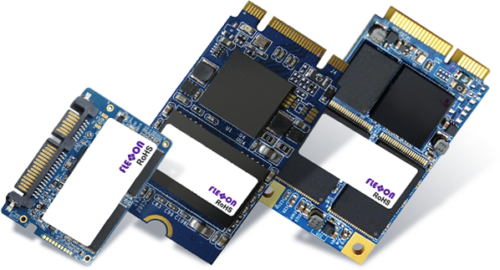
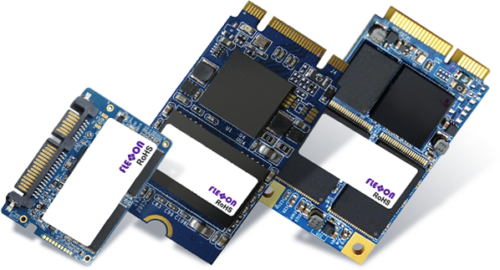
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
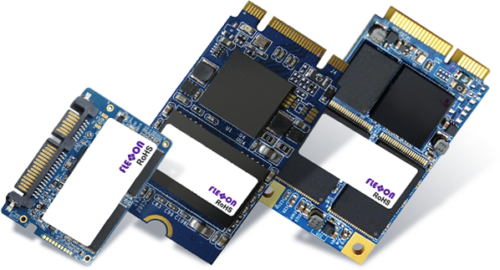
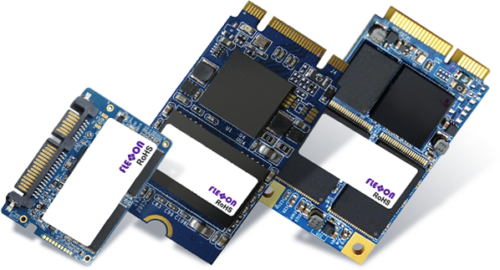
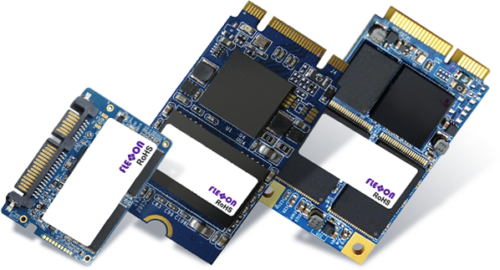
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
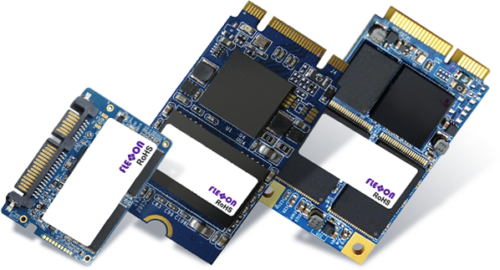
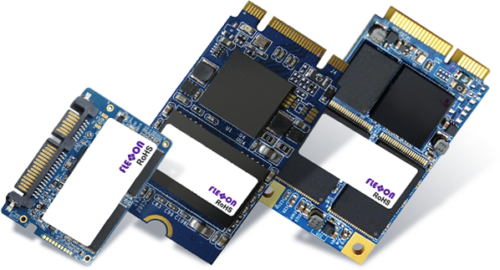
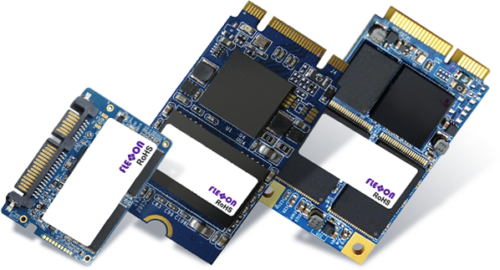
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -

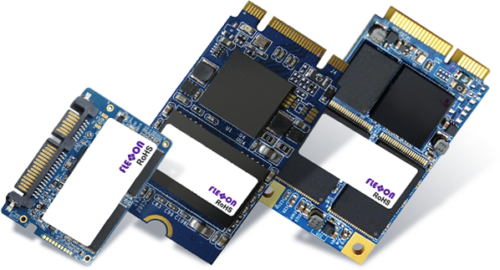
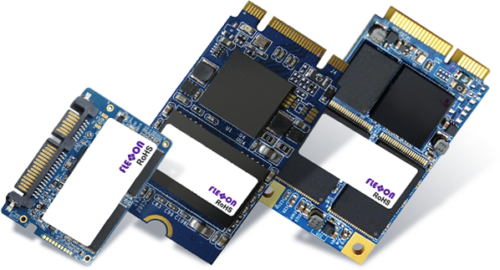
About secureSYSTM Technology
The secureSYSTM is a unique configuration combined with the power of patent-pending hardware protection. When in the locked state, the program files and operating system are completely read-only while still allowing full system performance in cache. All data is sent to the allocated data location. Imagine, a golden image that can?t be touched. Need to make changes and updates? No problem. Just insert the key.Part No. AVANT-D-1 -

About secureSYSTM Technology
The secureSYSTM is a unique configuration combined with the power of patent-pending hardware protection. When in the locked state, the program files and operating system are completely read-only while still allowing full system performance in cache. All data is sent to the allocated data location. Imagine, a golden image that can?t be touched. Need to make changes and updates? No problem. Just insert the key.Part No. AVANT-D-2 -

About secureSYSTM Technology
The secureSYSTM is a unique configuration combined with the power of patent-pending hardware protection. When in the locked state, the program files and operating system are completely read-only while still allowing full system performance in cache. All data is sent to the allocated data location. Imagine, a golden image that can?t be touched. Need to make changes and updates? No problem. Just insert the key.Part No. AVANT-D-3 -

About secureSYSTM Technology
The secureSYSTM is a unique configuration combined with the power of patent-pending hardware protection. When in the locked state, the program files and operating system are completely read-only while still allowing full system performance in cache. All data is sent to the allocated data location. Imagine, a golden image that can?t be touched. Need to make changes and updates? No problem. Just insert the key.Part No. AVANT-MD1 -

About secureSYSTM Technology
The secureSYSTM is a unique configuration combined with the power of patent-pending hardware protection. When in the locked state, the program files and operating system are completely read-only while still allowing full system performance in cache. All data is sent to the allocated data location. Imagine, a golden image that can?t be touched. Need to make changes and updates? No problem. Just insert the key.Part No. AVANT-MD-2 -

About secureSYSTM Technology
The secureSYSTM is a unique configuration combined with the power of patent-pending hardware protection. When in the locked state, the program files and operating system are completely read-only while still allowing full system performance in cache. All data is sent to the allocated data location. Imagine, a golden image that can?t be touched. Need to make changes and updates? No problem. Just insert the key.Part No. AVANT-MD-3 -
 The CyberD RJ45 Lock Key is used to unlock the CyberD RJ45 Port Lock.
The CyberD RJ45 Lock Key is used to unlock the CyberD RJ45 Port Lock.Keys and locks must be the same color for successful removal.
Part No. CD35101 -
 The CyberD RJ45 Port Lock prevents unapproved connection to an open RJ45 port. Key NOT included Requires one CyberD RJ45 Lock Key for removal. Keys and locks must be the same color for successful removal. Part No. CD35201
The CyberD RJ45 Port Lock prevents unapproved connection to an open RJ45 port. Key NOT included Requires one CyberD RJ45 Lock Key for removal. Keys and locks must be the same color for successful removal. Part No. CD35201 -
 The CyberD SFP Lock Key is used to unlock the CyberD SFP Port Lock.
The CyberD SFP Lock Key is used to unlock the CyberD SFP Port Lock.Keys and locks must be the same color for successful removal.
Part No. CD34101 -
 The CyberD SFP Port Lock prevents unapproved connection to an open SFP port. Key NOT included Requires one CyberD SFP Lock Key for removal. Keys and locks must be the same color for successful removal. Part No. CD34201
The CyberD SFP Port Lock prevents unapproved connection to an open SFP port. Key NOT included Requires one CyberD SFP Lock Key for removal. Keys and locks must be the same color for successful removal. Part No. CD34201 -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD.
Ensure a tamper-proof data storage solution by making it unalterable to keep the crucial files safe with Flexxon Read-Only Mode SSD. Once you activate the Read-Only mode into the SSD, all the stored data enables access for reading only and none can change, delete, or overwrite anything. Preserve the authenticity of essential files and prohibit the risk of alteration with the Read-Only Mode SSD. -
 With this neat little device, system administrators can physically prevent users from connecting Flash Drives, MP3 Players and other USB Mass Storage Devices to their computers to copy data, introduce viruses etc.The USB Port Blocker is made up of a combined key' and 'block' assembly which plugs into the USB port. To use, simply plug the 'keyblock' into the port and release the latch—the block remains in place! Plug the key back into the block to remove. Easy!Part No. 40450
With this neat little device, system administrators can physically prevent users from connecting Flash Drives, MP3 Players and other USB Mass Storage Devices to their computers to copy data, introduce viruses etc.The USB Port Blocker is made up of a combined key' and 'block' assembly which plugs into the USB port. To use, simply plug the 'keyblock' into the port and release the latch—the block remains in place! Plug the key back into the block to remove. Easy!Part No. 40450 -
 With this neat little device, system administrators can physically prevent users from connecting Flash Drives, MP3 Players and other USB Mass Storage Devices to their computers to copy data, introduce viruses etc.The USB Port Blocker is made up of a combined key' and 'block' assembly which plugs into the USB port. To use, simply plug the 'keyblock' into the port and release the latch—the block remains in place! Plug the key back into the block to remove. Easy!Part No. 40451
With this neat little device, system administrators can physically prevent users from connecting Flash Drives, MP3 Players and other USB Mass Storage Devices to their computers to copy data, introduce viruses etc.The USB Port Blocker is made up of a combined key' and 'block' assembly which plugs into the USB port. To use, simply plug the 'keyblock' into the port and release the latch—the block remains in place! Plug the key back into the block to remove. Easy!Part No. 40451 -
 With this neat little device, system administrators can physically prevent users from connecting Flash Drives, MP3 Players and other USB Mass Storage Devices to their computers to copy data, introduce viruses etc.The USB Port Blocker is made up of a combined key' and 'block' assembly which plugs into the USB port. To use, simply plug the 'keyblock' into the port and release the latch—the block remains in place! Plug the key back into the block to remove. Easy!Part No. 40452
With this neat little device, system administrators can physically prevent users from connecting Flash Drives, MP3 Players and other USB Mass Storage Devices to their computers to copy data, introduce viruses etc.The USB Port Blocker is made up of a combined key' and 'block' assembly which plugs into the USB port. To use, simply plug the 'keyblock' into the port and release the latch—the block remains in place! Plug the key back into the block to remove. Easy!Part No. 40452 -
 With this neat little device, system administrators can physically prevent users from connecting Flash Drives, MP3 Players and other USB Mass Storage Devices to their computers to copy data, introduce viruses etc.The USB Port Blocker is made up of a combined key' and 'block' assembly which plugs into the USB port. To use, simply plug the 'keyblock' into the port and release the latch—the block remains in place! Plug the key back into the block to remove. Easy!Part No. 40453
With this neat little device, system administrators can physically prevent users from connecting Flash Drives, MP3 Players and other USB Mass Storage Devices to their computers to copy data, introduce viruses etc.The USB Port Blocker is made up of a combined key' and 'block' assembly which plugs into the USB port. To use, simply plug the 'keyblock' into the port and release the latch—the block remains in place! Plug the key back into the block to remove. Easy!Part No. 40453 -
 With this neat little device, system administrators can physically prevent users from connecting Flash Drives, MP3 Players and other USB Mass Storage Devices to their computers to copy data, introduce viruses etc.The USB Port Blocker is made up of a combined key' and 'block' assembly which plugs into the USB port. To use, simply plug the 'keyblock' into the port and release the latch—the block remains in place! Plug the key back into the block to remove. Easy!Part No. 40454
With this neat little device, system administrators can physically prevent users from connecting Flash Drives, MP3 Players and other USB Mass Storage Devices to their computers to copy data, introduce viruses etc.The USB Port Blocker is made up of a combined key' and 'block' assembly which plugs into the USB port. To use, simply plug the 'keyblock' into the port and release the latch—the block remains in place! Plug the key back into the block to remove. Easy!Part No. 40454